This question has two very different answers: one is about types of proxy servers, the other is about proxy server protocols.
Let’s start with the types of proxy servers:
Reverse proxy: You don’t know you’re connecting to one, but it has the power to collect the data you need from several websites before returning it to you – kind of like “combined shipping” for the web.
Web proxy server: Acting as a load balancer, it spreads incoming requests over several servers to keep the service up. That way, a big influx of requests doesn’t crash the server.
Anonymous proxy: Hides your original IP address, but not the fact that a proxy is in use.
High anonymity proxy: hides both the original IP and the fact that you’re using a proxy.
Transparent proxy: Chances are that your boss is running one of those. A transparent proxy doesn’t modify your online requests, but it can monitor what you do. It can also be used to restrict access to websites your boss doesn’t want you to visit.
CGI proxy: This technology connects to a proxy via a website. You go to a
CGI proxy website, enter the address of another website into the web form, and the proxy website then displays it for you. It’s like a browser within a browser.
Suffix proxy: This proxy adds its own suffix to the website’s address to overcome firewall filters… However, modern filters can usually block it.
Distorting proxy: It will identify itself as a proxy server but give a false IP address of the client if asked.
DNS proxy: You’ll most often encounter “DNS proxy” as a service that only routes your traffic via a proxy for specific purposes, like accessing websites.
Now, aside from these types of proxy servers, there are also proxy protocols – sets of digital communication rules defining the way they are configured.
Here are the different proxy protocols:
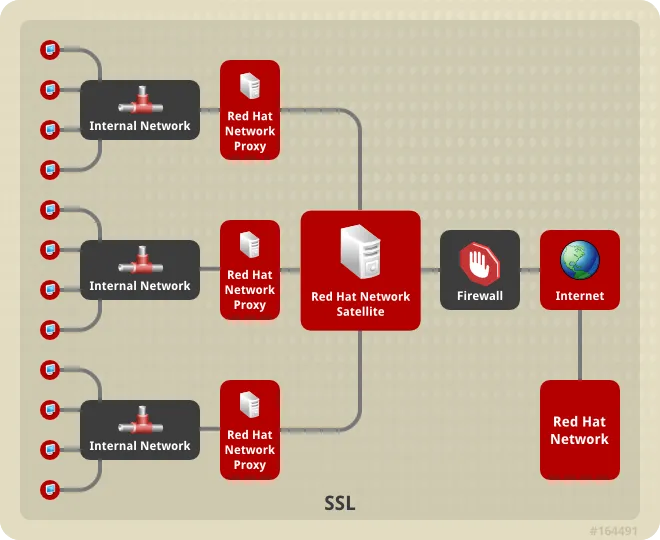
SSL: Secure Sockets Layer is a proxy protocol used to protect your data during transmission, such as when you make a transaction during an online purchase.
FTP: File Transfer Protocol proxy is used when you’re uploading data to a server, such as when you upload your pictures to the cloud or add music files to online music services. An FTP proxy can offer enhanced security for your uploaded files.
HTTP: A hypertext transfer protocol proxy caches web pages and files so that you can access them faster on sites that you visit frequently. But if the cache builds up too much, it can ultimately slow down your browsing, so it is recommended that you clear your cache on a regular basis.
SOCKS: Often upgraded with additional security measures to make it undetectable, SOCKS communicates to the proxy server on a level lower than HTTP to overcome firewalls. Famously a part of the Shadowsocks protocol.